Recently, one of our clients contacted about something rather strange: a ”language” value in his newly Google Analytics setup that stated: ”Secret.ɢoogle.com You are invited! Enter only with this ticket URL. Copy it. Vote for Trump!”
Of course, we all know that browser headers/requests can be easily altered, but we still wonder why Google allows such values in it’s [non-bot] visitor-related reports. And if it does some data validation / sanitizing or not really.
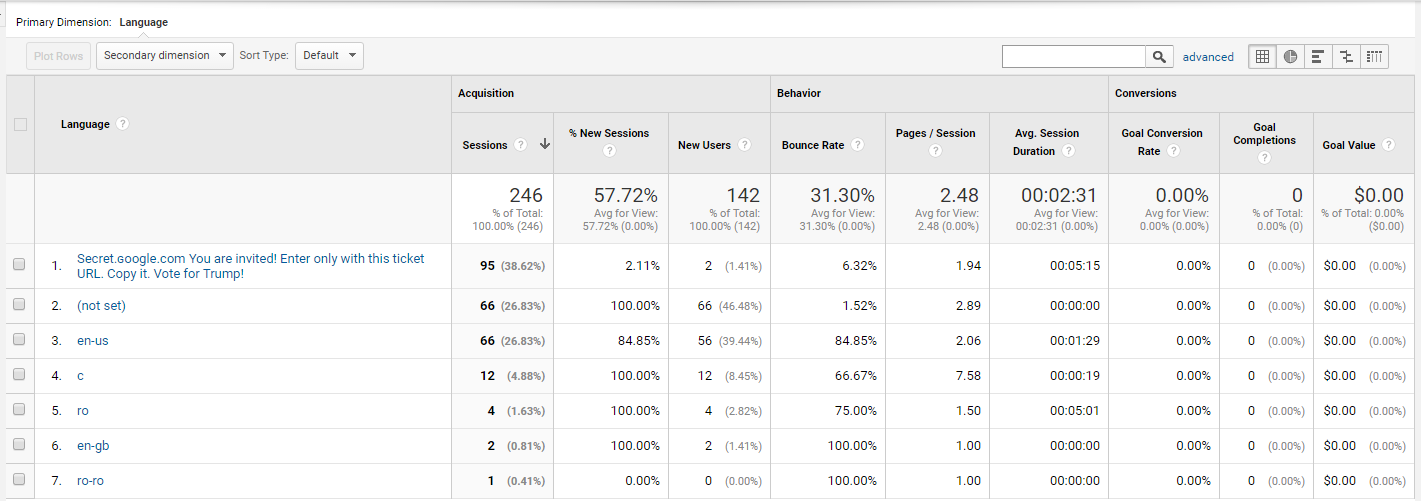
P.S. Beware that ”secret.ɢoogle.com” differs from ”secret.google.com”. Here are the ASCII code values:
Secret.ɢoogle.com: 115 101 099 114 101 116 046 201 162 111 111 103 108 101 046 099 111 109
secret.google.com: 115 101 099 114 101 116 046 103 111 111 103 108 101 046 099 111 109